Jun 26th, 2017 - Category: Miscellaneous
(Due to a large number of requests, this is single post that contains all 13 parts of the series.)
Part 1 - Introduction
 People are afraid of online threats for good reasons. We use computers and the internet for everything from banking to social communication to storing cherished family photos and videos. So many devices are portable, which can result in additional security issues. This series of posts will present a variety of simple and practical techniques to stay safe from the worst online threats such as malware (aka viruses) from infected websites and “phishing” emails, online account hacking, and the dangers involved when using public WiFi hotspots. It will also include an introduction to the terminology and symptoms of malware, hopefully making it a bit easier to figure out if a computer or online account has been compromised. It will conclude with suggestions for creating strong and memorable passwords. Each post will be relatively short and a deeper discussion will follow in future posts.
People are afraid of online threats for good reasons. We use computers and the internet for everything from banking to social communication to storing cherished family photos and videos. So many devices are portable, which can result in additional security issues. This series of posts will present a variety of simple and practical techniques to stay safe from the worst online threats such as malware (aka viruses) from infected websites and “phishing” emails, online account hacking, and the dangers involved when using public WiFi hotspots. It will also include an introduction to the terminology and symptoms of malware, hopefully making it a bit easier to figure out if a computer or online account has been compromised. It will conclude with suggestions for creating strong and memorable passwords. Each post will be relatively short and a deeper discussion will follow in future posts.
 The problem for most of us is that the official definitions are unnecessarily complex. For example, the definition for malware is “Parasitic software fragments that attach themselves to some existing executable content. The fragment may be machine code that infects some existing application, utility, or system program, or even the code used to boot a computer system.” This definition means practically nothing to non-technical people. Actually, it’s possible to ignore most of the techno jargon, but knowing a few basic terms is necessary because even a Google search requires knowing a few right words.
The problem for most of us is that the official definitions are unnecessarily complex. For example, the definition for malware is “Parasitic software fragments that attach themselves to some existing executable content. The fragment may be machine code that infects some existing application, utility, or system program, or even the code used to boot a computer system.” This definition means practically nothing to non-technical people. Actually, it’s possible to ignore most of the techno jargon, but knowing a few basic terms is necessary because even a Google search requires knowing a few right words.
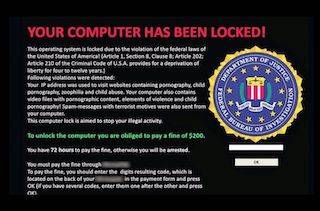
More simply put, malware is the general term for computer viruses, worms, trojan horses, ransomware, spyware, adware, scareware, rootkits, and other malicious programs. The details of each of these types of malware will be provided in a future post, but for now it helps to learn the obvious symptoms of malware so it can be removed as soon as possible. Ransomware is the easiest to identify since the point of this malware is to tell the user they have been infected. The cyber criminal scrambles the files and will not unscramble them until the ransom is paid (if ever). Some messages even make it sound like the user has broken federal laws (you can’t even believe criminals these days!).
Part 2 - Introduction (continued)
However most malware is typically more subtle. A common sign of infection is when an internet browser (Internet Explorer, Edge, Chrome, Safari, etc.) displays a different website than the user types in. This can also happen to links clicked on from a Google search. The technical terms for this malware include a “browser redirect virus” or “browser hijacker.” It can also change the homepage, add new toolbars, display advertising, and create pop-up messages even when not online.
Other signs can include a computer that suddenly runs very slowly, constantly crashes / freezes, or if a user discovers new icons that appear on the desktop. Malware is a very complex topic, it can be difficult to detect and remove even for experts. Worse still, it can include spyware that steals passwords and emails itself to others so it’s obviously best to avoid getting it in the first place.
One key to avoiding malware is to think before clicking on any link online. Dangers can include free software downloads, links on shady websites of all types, downloading a “required” video player, and clicking on online ads. Even plugging in a friend’s USB memory stick can deliver malware. Another way it can be installed is through something called “social engineering” where a user is tricked into clicking on a dangerous link through a carefully written fake email, text, or instant message. These messages are also known as “phishing campaigns” and they can be VERY convincing (even coming from friends).
To summarize, here are a few tips for avoiding malware. Keep in mind that each of these suggestions could be expanded into an entire post!
- Make sure computer and phone software is kept up to date (if you’re still on Windows 95, you’re really in trouble).
- Never click on links or open attachments in messages from unknown sources. Unexpected messages from known sources should be also be treated with suspicion since some viruses can access a user’s email and send a message to friends in their entire address book.
- Never click on links in emails from banks, Apple, Google, Microsoft, etc. Access the website directly.
- Backup regularly! Backups are an effective way to recover from digital and physical disasters if the 321 rule is used: three full backups on two different types of media with one copy stored “somewhere else” (more details in a future post).
- On Windows, at least use Windows Defender (anti-virus software is a massive topic on its own).
- Use strong / unique passwords and a password manager. Two factor authentication is an advanced technique that is also very effective for securing critical accounts such as email, banking, and social media (another topic for a future post).
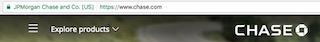
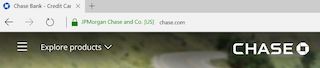
- Look for secure connections to websites (the padlock symbol = HTTPS) and logout when done. The padlock is in different places on different computers / browsers. Some examples are below.


Additional Resources:
- Glossary
- General Articles
- Symptoms
- Google Safe Browsing
- Google Malware Efforts
- Google Malware Video
- Are Antivirus programs bad?
- Phone Malware (more in a future post)
Part 3 - More About Passwords
These days, almost everybody has dozens of online accounts most of which are tied to their email address. It is tempting to reuse the same ‘easy to remember’ password but securing online accounts such as banking, email, Facebook, App Stores, and others with strong, unique passwords is critical to staying safe online. Email accounts are especially tempting targets for hackers because they not only provide the usernames for other accounts, but they also can be used to reset passwords and spread malware to other users.
For example, as reported in the news last December, hackers currently have data on over 1.5 billion Yahoo accounts. The Wikipedia article states that in the first part of the attack “The hackers had obtained data from over 500 million user accounts, including account names, email addresses, telephone numbers, dates of birth, hashed passwords, and in some cases, encrypted or unencrypted security questions and answers.” Hashed passwords can be translated as encrypted passwords, but to make a long story short, easy to guess passwords such as ‘123456 or qwerty’ are so common that hackers don’t even need to break the encryption.
Since user names are known by many other terms such as account name, user, user ID, email, login, login id, and screen name, this Yahoo data is an excellent starting point for more serious hacking. However, finding the time to change passwords is a daunting task. Each website’s password change option is in a different place and requires entering the old and new passwords. Then the new password has to be recorded somewhere safe. In a family, some of these new passwords also have to be available to others.
 The good news is that the change doesn’t have to be done all at once. It is easier to start with the most critical accounts such as email, banking, computer locking, and cell phone passcodes. Next other accounts can be updated such as social media, utilities, games, etc. little by little as they are used. The problem then becomes how to safely store those passwords. Many people store them in a small notebook next to their computer or in a text file on the desktop named PASSWORD.TXT. Please do not do that! The next post will provide several options for storing and automatically entering safe, strong passwords. As a teaser, if you don’t mind paying less than the cost of a latte a month, try 1Password from AgileBits. It can automatically securely store, enter, and share passwords. Ahhh, finally a world where only ‘1Password’ has to be remembered! (https://agilebits.com).
The good news is that the change doesn’t have to be done all at once. It is easier to start with the most critical accounts such as email, banking, computer locking, and cell phone passcodes. Next other accounts can be updated such as social media, utilities, games, etc. little by little as they are used. The problem then becomes how to safely store those passwords. Many people store them in a small notebook next to their computer or in a text file on the desktop named PASSWORD.TXT. Please do not do that! The next post will provide several options for storing and automatically entering safe, strong passwords. As a teaser, if you don’t mind paying less than the cost of a latte a month, try 1Password from AgileBits. It can automatically securely store, enter, and share passwords. Ahhh, finally a world where only ‘1Password’ has to be remembered! (https://agilebits.com).
Part 4 - Even More About Passwords
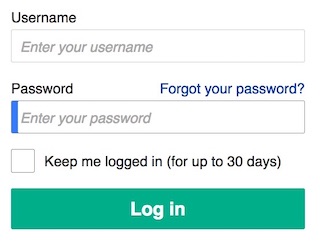 As explained in the last post in this series, a good password manager is critical to staying safe online. It is also the key to working efficiently. With more and more websites requiring a new login each time they are used, the lowly username screen has become a source of stress for many.
As explained in the last post in this series, a good password manager is critical to staying safe online. It is also the key to working efficiently. With more and more websites requiring a new login each time they are used, the lowly username screen has become a source of stress for many.
Luckily, there are many options and here is a summary of the best of them.
1Password is definitely at the top of the list and well worth the small cost of $3 a month. It works on MacOS, iOS, Android, and Windows devices and can synchronize passwords between them. It even has a family plan for $5 a month that can organize shared passwords while still allowing each member to store private ones in the same account. As a bonus, it can store much more than passwords, including WiFi logins, credit card information, drivers license, and secure notes. Finally, it has a well written tutorial for new users that can be found here.
The next option is for MacOS / iOS users and is called iCloud Keychain. Apple’s free solution is great due to the integration with their default browser Safari. Once turned on, it fills in passwords automatically, suggests strong passwords for new websites, offers to save existing passwords, and synchronizes passwords between devices logged into the same iCloud account. It can also securely store and fill in credit card information to making online shopping quicker. The website 9to5Mac recently published a post on iCloud Keychain that is worth reading, “iCloud Keychain and Answering Your Common Password Management Concerns.”
For Windows users, Microsoft’s Edge browser built-in password management is fine too. For complex reasons, it is a little less secure than professional solutions, but better than nothing. The biggest drawback is that it cannot synchronize passwords between Windows and a mobile device like an iOS or Android phone.
Finally, KeePass is a free and open source password manager, but more complex to install and use. You can find it at http://keepass.info/.
There is a constant stream of online articles on the best practices for password management. The 9to5Mac posts, “How to Approach and Manage Passwords” and “How to Implement and Benefit From Password Management Software” dive deep into the subject. For people short on time, they both end with an excellent summary simply called, “Do This.” So what are you waiting for? Do This!!!
Part 5 - How Secure is an iPhone? Really Secure!
Today many people carry their entire digital life around in their smartphones. Emails, text messages, address books, calendars, to do lists, banking apps, music, and photos are just a few of the valuable items found on these small slabs of metal and glass. This makes the humble cell phone an attractive target for hackers. Recently, the news has been filled with stories about smartphone security. This is a result of the fact that the president was known to have been using an ancient, insecure Android phone from 2012 (Samsung Galaxy S3). He finally upgraded to an iPhone this week.
Why was an iPhone chosen for the President of the United States? Probably because it’s the most secure phone on the market today. It is amazing the lengths Apple goes to and they do it without much fanfare. Buried toward the end of the iOS webpage is a section called “Privacy and Security” with a short paragraph on security:
iOS offers the most advanced security of any mobile operating system. For starters, hardware and firmware features are designed to protect against malware and viruses, while iOS features help to secure your personal information. Touch ID lets you use your fingerprint as an easy alternative to entering your passcode each time, preventing unauthorized access to your device. And we give developers tools to make the safest apps possible, including top-notch encryption, app transport security, and more. The point is, security runs throughout the entire system — everything from the hardware to iOS to the App Store.
 Deep down though, iOS security is hidden universe of its own. The IOS Security Guide explains the details in 63 pages and there is an interesting lecture on Apple’s Developer website that covers the highlights in 25 minutes. To make a long story short, since Apple has control of both the iPhone hardware and iOS software, they can insure security from the moment the iPhone is turned on and even when it is turned off. They don’t even allow downgrading iOS software since that would make a secure iPhone insecure. Also, each iPhone has a completely separate security microprocessor called the “Secure Enclave Processor”(SEP) that includes a unique code burned into it. This means that only your iPhone can decrypt your data. Finally, Apple enforces its commitment to security on its App developers as well as on how a device securely communicates with the outside world.
Deep down though, iOS security is hidden universe of its own. The IOS Security Guide explains the details in 63 pages and there is an interesting lecture on Apple’s Developer website that covers the highlights in 25 minutes. To make a long story short, since Apple has control of both the iPhone hardware and iOS software, they can insure security from the moment the iPhone is turned on and even when it is turned off. They don’t even allow downgrading iOS software since that would make a secure iPhone insecure. Also, each iPhone has a completely separate security microprocessor called the “Secure Enclave Processor”(SEP) that includes a unique code burned into it. This means that only your iPhone can decrypt your data. Finally, Apple enforces its commitment to security on its App developers as well as on how a device securely communicates with the outside world.
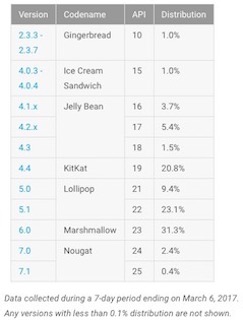
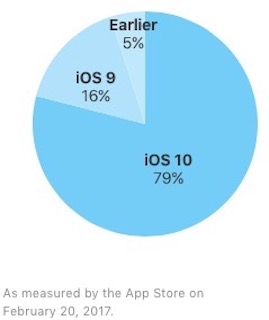 To be fair, Google / Android does care about security and implements many of the same measures in the most recent versions, but only 3% of Android users have upgraded compared to 80% of iOS users. Apple’s security philosophy is a great example of something called “layered security” which professionals recommend as the best practice to stay safe online. A future post in this series will explore layered security in detail.
To be fair, Google / Android does care about security and implements many of the same measures in the most recent versions, but only 3% of Android users have upgraded compared to 80% of iOS users. Apple’s security philosophy is a great example of something called “layered security” which professionals recommend as the best practice to stay safe online. A future post in this series will explore layered security in detail.
Part 6 - A Few Words About Online Privacy
A recent podcast on Recode, “How do I protect my privacy online?” featured digital security expert Tony Gambacorta answering questions about online security and privacy. He said, “The greatest threat is our own ignorance.” In terms of security, on the top of his list were many of the topics that are already in this series of posts, but the part about privacy was particularly interesting. In terms of privacy, his biggest concerns focus on the so-called Internet of Things (IoT) devices such as Amazon Echo, Google Home, and “smart home” cameras, thermostats, light controllers, security systems, Smart TVs, etc.
These are devices that provide useful features in return for legal access to what most consider their private world such as conversations and activities in their home. For example, some people cover their laptop webcam with tape when their Smart TV has an embedded camera and microphone controlled by much less secure software. Many WiFi cameras that are used to monitor a home fall into this insecure category. Gambacorta also explains that a $20 device can be used in a coffee shop to anonymously eavesdrop on unencrypted web searches, emails, etc. For these reasons, a VPN service is critical when using public WiFi and will be explained in detail in a future post, but in general avoid free VPNs, they are often free because they are not private.
![]() His privacy suggestions for people who aren’t tech-literate?
His privacy suggestions for people who aren’t tech-literate?
- Don’t put something like a WiFi camera or Smart TV in a sensitive area of your house (or put tape on the lens).
- Buy from people you know and trust. Buying a $70 Android phone from a user called “ThePhoneBoss” on eBay might not be the best choice for security or privacy.
- Email is never private (unless you’re an expert).
- Use your browser’s “Incognito” feature if you are searching for anything you wouldn’t want somebody else to know about (or something that you don’t want to see ads about in the future). This is also known as a “Private” or “InPrivate” window. As the graphic below shows, it is shocking how little privacy is involved when web surfing.
Well, that’s more than a few words, but let’s just keep that between you and me…
Part 7 - Techniques for Layered Security
Before we start on what sounds like a boring topic, here’s a story that should help make it more interesting.
After work, Dan decides to indulge in a quiet cup of coffee in his favorite local shop with free Wifi. Opening his laptop, he notices a guy nearby hunched over working intently on a laptop. He must be a hardcore techie because his computer is covered with stickers and has a small antenna attached to it. The heavy metal band logo on his hoodie confirms Dan’s suspicions. A moment later, a beep from Dan’s phone reminds him that he has at least a dozen personal messages to read so he connects to the first network on the list “Free Coffee Shop WiFi.”
As he waits for the webpage to load, he thinks, “How strange, yesterday it was just called Coffee Shop WiFi, maybe they want people to know that it’s really free?” Soon he sees the familiar login page and signs into Gmail. It rejects his password. That’s also strange, he was so careful to type it correctly. He enters it again and it works. Annoyed now, he chalks it up to his new crazy complex password that he is using for his most valuable accounts. “Oh well, can’t be too safe these days.” Somebody at work suggested a password manager, but who has time for that nonsense. Besides, typing it once a month is no big deal.
You probably know where this story is going. Dan has just been hacked and his Gmail login and password stolen. As soon as he leaves, the hacker will change it to prevent Dan from getting back in and try to access his bank, social media, etc. Dan won’t get the warning emails because he can’t access his account anymore. The hacker has reported his phone lost and erased it remotely.
Hopefully, this story demonstrates the need for something security professionals call “layered security.” It’s actually not that hard to implement. Earlier parts of this series have already discussed parts of the technique such as confirming the website address in the browser, HTTPS security, strong/unique passwords, and using a password manager. In this case, a password manager would have prevented the hacker from stealing Dan’s password. How? Since it wouldn’t have entered the password because the hacker’s fake login screen wouldn’t have matched the website used when the password was stored. A password manager can also prevent a hacker from video recording Dan’s fingers typing his password. Oh, those clever hackers!
To wrap up this post, below is a summary of the layers of security involved in Dan’s sad story and the associated parts of this series of posts.
- Part 8 - The next post will explain why a Virtual Private Network (VPN) should always be used on public Wifi to avoid others eavesdropping. Remember, most of the time hackers are not looking to hack you personally, they are looking for easy targets.
- Part 3 - Never reuse passwords across sensitive accounts.
- Part 2 - Look for secure connections to websites (the padlock symbol = HTTPS) and logout when done.
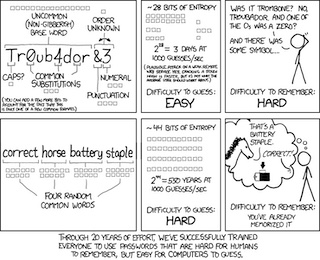
- Part 4 - Use a password manager and secure it with a unique, very strong password. Below is a comic strip that explains how and why courtesy of XKCD.
- Part 10 - Use something called two factor authentication (2FA) to secure your most sensitive accounts. 2FA stops hackers by requiring “two factors” to login, typically something you know (such as a password) and something you have such as your cellphone (a code received as a text message).
Part 8 - Being Safe on Public WiFi with a VPN
 Four years ago I wrote a post about the risks involved in using Public Wifi called “The Good, the Bad, and the Ugly.” While the information is still current, the suggestion to use a VPN has only recently reached mainstream awareness. This is due to Congress voting to allow Internet Service Providers (ISP) to sell users’ browsing data. Now the market for VPNs has exploded creating a confusing array of options. Even worse, most people don’t even know what VPN stands for much less how it provides security and protects privacy.
Four years ago I wrote a post about the risks involved in using Public Wifi called “The Good, the Bad, and the Ugly.” While the information is still current, the suggestion to use a VPN has only recently reached mainstream awareness. This is due to Congress voting to allow Internet Service Providers (ISP) to sell users’ browsing data. Now the market for VPNs has exploded creating a confusing array of options. Even worse, most people don’t even know what VPN stands for much less how it provides security and protects privacy.
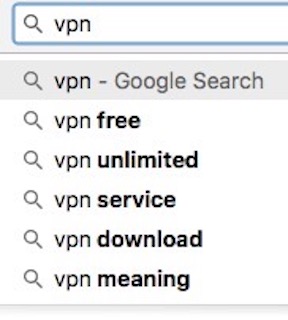
VPN stands for Virtual Private Network and it means that when you connect, your data is encrypted (i.e., safe and private). However beyond the basic definition, even a Google search is a bit misleading on how to use one. As the graphic shows, the first suggestion is “VPN Free” and experts agree that completely free VPN is worth what you pay for it… nothing! These search results point to companies that sell your private browsing information to make money. So a VPN not only has to work technically, but it has to be backed by an ethical company. Remember, poor Dan from the last post of this series would have been safe from hackers if he had used a reputable VPN. After connecting, his next step would have been to activate the VPN (some “persistent” VPNs even do this automatically). A hacker cannot intercept data encrypted by a VPN, it just looks like random characters.
 But finding a reputable VPN company is tough because the VPN world has become a little like the anti-virus world, a confusing mess of spammy advertising posing as reviews. Also, certain VPNs are better for certain applications (privacy or security), usage levels, devices (Windows, Mac, Android, iOS, etc.), speed, and ease of use.
But finding a reputable VPN company is tough because the VPN world has become a little like the anti-virus world, a confusing mess of spammy advertising posing as reviews. Also, certain VPNs are better for certain applications (privacy or security), usage levels, devices (Windows, Mac, Android, iOS, etc.), speed, and ease of use.
After considerable research, the options below are a good starting point, especially the website “The Best VPN.” I didn’t believe this was a legit website at first either, but it has a very well written article on Public WiFi with an excellent infographic about a quarter of the way down. The first three suggestions (out of ten) are the best:
- Be mindful and proactive - Hackers can quickly plug in a flash drive with malware into an unattended computer or easily record video of keystrokes.
- Turn off “Sharing” - A complex topic, but the article outlines the steps
- Use a VPN - Of course! (don’t worry about Tor, that’s an advanced topic)
 Finally, keep in mind that the VPN world is changing quickly: websites with honest reviews can change hands and become biased, VPN providers can merge, and new options are appearing everyday. Do a little research and don’t signup for “lifetime” VPN subscriptions.
Finally, keep in mind that the VPN world is changing quickly: websites with honest reviews can change hands and become biased, VPN providers can merge, and new options are appearing everyday. Do a little research and don’t signup for “lifetime” VPN subscriptions.
Additional Resources:
- VPN with a “vacation” short-term pricing option - VPN Unlimited
- VPN with a 500 MB free option - TunnelBear
- VPN for general use - Private Internet Access
- Extensive “techie” comparison chart
- Article from the hacker’s perspective
- When VPNs Go Bad
- Good reference article
- The impossible tasking of making a VPN list
- Making your own VPN
Part 9 - Mobile Security
In 2016, a major anti-virus company reported that Android based malware packages had tripled in the past year to over 8.5 million. While this huge number is suspicious considering the source, i.e. a company that sells a subscription to their mobile security product for $15 a year, mobile malware is still an exploding issue. ArsTechnica is a good website for unbiased, in-depth analysis of mobile threats.
The biggest headlines from the past year have been concerning:
- 7/2016 - 10 million Android phones infected by all-powerful auto-rooting apps
- 11/2016 - 1 million Google accounts compromised by Android malware called Gooligan
- 1/2017 - Virulent Android malware returns, gets > 2 million downloads on Google Play
- 4/2017 - Android devices can be fatally hacked by malicious Wi-Fi networks
If you are not convinced yet, the website 9to5Google says that “A New Example of Android Malware is Discovered Every 10 Seconds.” Even an innocent game guide with cute graphics that your child downloaded can hide nasty malware called “Falseguide.”
In response, the security website Malwarebytes now has a section for mobile malware and the descriptions look like the traditional descriptions of malware with headings like: “Spyware, Potentially Unwanted Programs (PUPs), and Ransomware.”
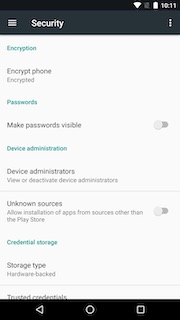 Malwarebytes also provides some best practices for avoiding these dangers. In a recent blog post, they strongly recommend only installing apps from the Google Play Store and blocking other App Stores by turning off the setting in Android called “Unknown Sources” (Settings > Security).
Malwarebytes also provides some best practices for avoiding these dangers. In a recent blog post, they strongly recommend only installing apps from the Google Play Store and blocking other App Stores by turning off the setting in Android called “Unknown Sources” (Settings > Security).
They also recommend Checking Permissions of installed apps. If that “innocent” game guide mentioned above pops up a permission request screen asking for full device admin rights, that’s a subtle clue that something is very wrong.
Another suggestion is to be wary of something they call “You Get What You Pay For.” This is also known as, “If You’re Not Paying, You’re the Product.” For example, Gmail is free for a reason. Google is making a lot of money from (anonymous) access to your emails. Google might be a good tradeoff for the valuable services they provide, but free VPN providers that sacrifice privacy, free games filled with ads, and free utilities that can kill battery life and use data are not worth the savings of $0.99.
If you are using an iPhone, 95% of the comments above don’t apply to you. This was discussed in the recent post, “How Secure is an iPhone.” While this could change, it would be front page news. Still, be careful with the permissions you give iOS apps and beware of freebies.
Finally, don’t forget to backup your phone and use strong passcodes! More about that in future posts, but for now at least activate cloud based backup for your iPhone (Settings > iCloud > iCloud Backup) or Android (Settings > Backup & Reset).
Additional Resources:
Making Your iPhone Safer and Android Malware Video
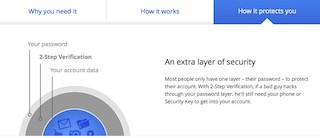
Part 10 - Is a Strong, Unique Password Enough?
Once you start down the rabbit hole of online security, it can seem endless. For example, as previously explained, strong passwords require a password manager to store them and then the password manager requires an even stronger password to keep those strong passwords secure. No less than three parts of this series of articles have been dedicated to passwords, but believe it or not, there is a growing movement toward something called “two factor authentication” that makes strong, unique passwords only one of the two things needed to login to critical accounts. It is so important that Apple even briefly considered making it mandatory for iCloud accounts so it is definitely worth understanding before deciding to use it.
 Unfortunately, it is a bit of a complex topic so let’s break it down into smaller parts.
Unfortunately, it is a bit of a complex topic so let’s break it down into smaller parts.
- What is it called? - The most common names are: Two-factor authentication (2FA), Multi-factor authentication (MFA), and Two-step verification.
- Why is it used? - Email is central to other security features of accounts and can be used to reset passwords for other accounts such as banking, shopping, etc. Cloud storage accounts contain valuable resources that are synchronized across devices. Deleting something “in the cloud” can delete it everywhere. 2FA makes these and other accounts like banking more secure.
- What is it? - 2FA requires a second step (factor) to login. These factors typically include knowledge (of a password), possession (of a smartphone), and inherence (of a fingerprint). 95% of the time a 2FA login requires entering the password and the code from a text message sent to a cellphone, but backup methods include a voice call, a code from a smart phone app tied to the account, a text message to a backup cellphone, or responding to a prompt after unlocking a cellphone with a fingerprint.
- How it protects? - Simply put 2FA increases safety by combining something you know, the password, with something you have, the smartphone.
- What are some dangers associated with 2FA? - A lost, stolen, broken, or hacked phone can make getting the code impossible so all 2FA systems have backup methods such as specifying a backup phone, printing a list of backup codes (recovery keys) and storing them in a physically safe place (not in a file on your computer!), or answering detailed security questions.
 As an additional step, it might be a good idea to keep an encoded list of passwords on a sheet of paper in a safe place. For example:
As an additional step, it might be a good idea to keep an encoded list of passwords on a sheet of paper in a safe place. For example:
- Power Company - jdoe@gmail.com - *bhr18$
- Cellphone - jdoe@gmail.com - #dcd22@
Where “*bhr18$” would stand for the real password “*beach-horse-ride18$” and “#dcd22@” would stand for “#desert-cat-drive22@” Creating strong passwords with a pattern like “place,” “animal,” and “action” can reduce confusion.
It may sound crazy to add yet another layer to the security of critical accounts, but once it is setup 2FA doesn’t add much effort to use. Both Google and Apple have excellent tutorials on setting up 2FA for their services.
Part 11 - To Go Forward You Must Backup
This silly quote used to be a trademark of the Dantz Corporation, the creators of one of the first backup solutions I used in the 1990’s called Retrospect. Those were the bad old days of tape backups costing thousands of dollars in hardware and software. Today it typically costs less than $60 to protect a computer’s priceless data such as photos, correspondence, and financial documents. That’s the price of a 1 TB portable USB external hard drive and the software is free with all modern computers. The process of setting up a backup system is also simple so if you’re not backing up your computer, stop what you are doing, visit your local office supply store or electronics store, and buy one.
 Welcome back. If you are using an Apple laptop or desktop computer, plugging the drive into a free USB port should automatically pop-up a window asking something similar to, “Do you want to use My Backup (1 TB) to back up with Time Machine?” Time Machine is Apple’s name for their free, built-in backup solution and “My Backup” is the name of the drive you just plugged in (so it might be different). It takes a couple hours for the first full backup to complete, but after that Time Machine works invisibly behind the scenes making a copy of every changed file every hour. This is not only great for recovering from rare major issues like a hard drive crash, but also for more common issues like an inadvertently deleted file.
Welcome back. If you are using an Apple laptop or desktop computer, plugging the drive into a free USB port should automatically pop-up a window asking something similar to, “Do you want to use My Backup (1 TB) to back up with Time Machine?” Time Machine is Apple’s name for their free, built-in backup solution and “My Backup” is the name of the drive you just plugged in (so it might be different). It takes a couple hours for the first full backup to complete, but after that Time Machine works invisibly behind the scenes making a copy of every changed file every hour. This is not only great for recovering from rare major issues like a hard drive crash, but also for more common issues like an inadvertently deleted file.
Amazingly, if you ever have to do a complete restore, it puts a computer back to the exact state it was in when the last snapshot was taken. It really is like a time machine! More details can be found on Apple’s support website (and the website 9to5Mac), but it is obviously super simple to setup and very powerful to use.
If you are using Windows 10, Microsoft has a similar option called “File History.” By default it only backs up files in a user’s home directory, but that is still very useful. To set it up, select the Start button, select Settings > Update & security > Backup > Add a drive, and then choose an external drive or network location for your backups. You can find more information on Microsoft’s website.
Unfortunately, a single backup is not sufficient to create a robust recovery system for digital and physical disasters. Most experts recommend using something called the 3-2-1 rule. This means three copies of all data are made on two different types of media with one copy stored “somewhere else” such as “in the cloud.” For example, to keep that wonderful photo of your kids with the family dog safe, one copy would be on your computer hard drive, a second copy would be on a backup drive, and a third copy would be stored “in the cloud” through a service like iCloud, Google Photos, Dropbox, or CrashPlan.
Personally, I use a combination of Dropbox to backup critical files, iCloud Photo Library to backup photos, and a series of three backup USB external drives that I swap weekly. Is this overkill? Maybe, but the few times I have had to restore a computer from a backup, it has been a godsend, saving a day of tedious work restoring files and settings. Also, while the extra security is nice, daily benefits include photos that automatically transfer from phone to computer and Dropbox files that can be accessed from a phone or tablet anytime, from anywhere.
Finally, while there are hundreds of options available to “recover” from malware, nothing beats reformatting a hard drive and restoring files from a known, good backup. Malware is devious and many malware removal companies are devious too. This last topic will be covered in the next part of this series on online scams, but if you are still reading this and haven’t backed up yet…
Part 12 - General Scams
If the wide variety of threats from malware, weak passwords, public Wifi, and mobile security weren’t enough, there are now scammers taking advantage of people by offering personalized service. For example, while ransomware was discussed in Part 2, some crooks distribute malware that includes a “tech support” number to call. Other criminals call users proactively, especially targeting the elderly and non-tech savvy, offering “free” support. This support includes stealing credit card numbers and installing additional malware at no extra charge. By the way, “Windows technical support” is never going to call with a warning about a virus!
“Social engineering” scams are not limited to malware. Here is a short list of the worst ones lately (and they’re changing all the time):
- Job Offer Scams - A $75k / year job working from home based on an email interview! Wow! Oh, but they need $472 to cover the cost of (fill in the blank) or they need your banking information to setup direct deposit.
- Reshipping Scams - Getting paid to reship products, but the goods are stolen and the payment never arrives.
- Payment / Overpayment Scams - That ugly velvet painting of Elvis sold online for $50! But the stupid buyer accidentally sent you a check for $500… “Please refund the balance. Here’s my Western Union account.” When you refund the overpayment, they reverse the original payment.
- Shipping Scams - A “valuable package” is stuck in customs, just send $100 to “release it.” PayPal has a whole page of their FAQ devoted to these crazy schemes.
- Friend Help Scams - If a 90 year old relative is stuck in Venezuela and needs $500 to get home, that’s probably a hacked email account.
- Mystery Shoppers, Free Vacations and All “Too Good to Be True” Scams - If it sounds too good to be true, then it is.
- Technical Support Scams -
 Your browser cannot tell that you have a virus. It can however tell you that you have visited a “malicious site.” That is a legitimate warning.
Your browser cannot tell that you have a virus. It can however tell you that you have visited a “malicious site.” That is a legitimate warning. - App Store Scams - Signing up for a free trial of X triggers a prompt to subscribe. Tap the button to approve it by mistake and… “You will pay $99.99 for a 7-day subscription starting Jun 9, 2017.”
By the way, Robocallers are at the core of many of the scams above. I’ve started using Nomorobo, which is a great service to prevent Robocallers from getting through (there are many other options though).
Despite the length of this post, almost all of these scams boil down to using common sense: please send $500 to this Western Union account and you too can own the Brooklyn Bridge! LOL
Part 13 - Summary and Final Thoughts
After almost five months, we have arrived at the last part of this series and what a long, strange trip it has been. If you’ve made it this far, I hope you found this series interesting and useful. There are literally thousands of other suggestions for staying safer online, but the best seem to stay just short of paranoia while implementing reasonable security methods. For example, it’s worth providing one final reminder that ALL emails are insecure and links in them should be considered unsafe. Use bookmarks; type the site name; Google the site name (but don’t click on the ad please); etc. Think before you click! Never open attachments from unknown sources or click on suspicious looking pop up messages. Even if you recognize the name of the sender, if the email seems to come from “out of left field,” check the email address of the sender to see if it is real. You can protect yourself from many attacks by staying aware.
As far as anti-virus programs go, if good, layered security practices are used, the basic software that comes with a recent computer can be sufficient, i.e. Windows 10 Defender + Firewall and MacOS Internal Security + Firewall. The Wikipedia article on Anti-Virus software points out in the section “Issues of Concern” that anti-virus solutions can be as bad as the viruses they are supposed to be protecting against.
 Where can you get help that isn’t a scam in itself? Malwarebytes seems to be one of “the good guys” and their forums are a VERY active source of support. Piriform also seems to be legit with good software for removing malware called CCleaner. When a strange message pops up, doing a Google image search for “fake virus warnings” can also be helpful.
Where can you get help that isn’t a scam in itself? Malwarebytes seems to be one of “the good guys” and their forums are a VERY active source of support. Piriform also seems to be legit with good software for removing malware called CCleaner. When a strange message pops up, doing a Google image search for “fake virus warnings” can also be helpful.
Again, the key is to not be too paranoid or too complacent. People who write articles about security make money when others click on their links, so it literally pays to scare people into clicking and reading. Keep in mind that most people are not important enough to get hacked and if they were, a dedicated hacker, like a professional burglar, would be able to do it. The risks are in opportunistic hacking, i.e., leaving the back door open. The hacker thinks, “If I infect 1,000 computers and one person pays, great, that was a success.”
Finally, if you’re reading this and still don’t have a backup system in place, just remember “To go forward, you must backup!!!” $60 is a small price to pay or maybe you want to retake that photo of you with your dog from 20 years ago. You could borrow the neighbor’s dog and regrow those sideburns…